2FA OTP Authentication using OpenSource application, privacy included
How to protect your privacy when using 2FA OTP
Now that GitHub (Microsoft) decided that I absolutely need a 2FA to access my repositories, I decided to look for an OTP tools that respect privacy.
I'm looking for 2FA applications that can run on the Smartphone and are, if possible, open source.
As you can imagine the standard solutions of G8gle and Microsoft are privacy not included.
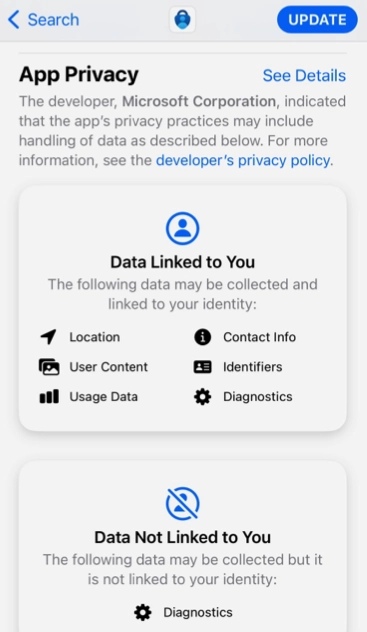
Here are a couple of screenshots from the Apple store for the 2 authenticators:
Microsoft Authenticator:
G8gle Authenticator:
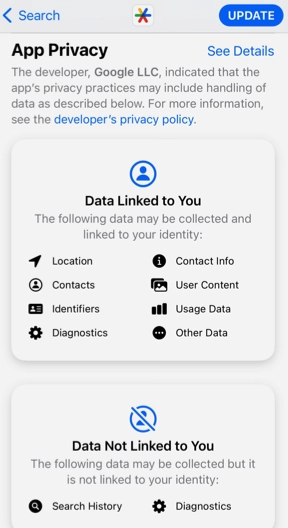
There are no doubts that my location, my contacts, my search history, the content of my device, and other data(?) are essential to login in GitHub and be sure that it's me.
But I prefer to maintain everything simple and let the owner of my phone and my passcode have access to my GitHub.
2FA OTP OpenSource to the rescue
After a quick research, I found this 2FA applications that are currently maintained and open source:
FreeOTP is distributed by RedHat and available for iOS, Android, and F-Droid:
https://freeotp.github.io
If you prefer a native solution here you have a couple of solutions.
Aegis - Android
For Android you can use Aegis, it is available on F-Droid: https://getaegis.app/
I didn't test this solution yet, but it seems very appreciated in the community.
Raivo OTP - iOS
For iOS there is an OpenSource application developed in Swift:
Raivo OTP (https://github.com/raivo-otp)
Raivo allows the synchronization of your properties using iCloud.
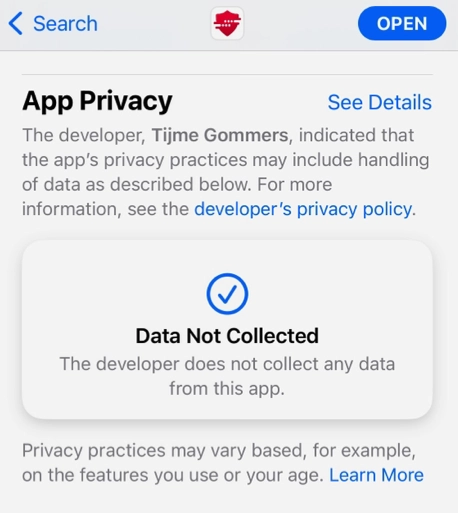
For example, you can see the 'privacy requirements' of Raivo compared to the mainstream tools.
... and andOTP?
Many 'old' pages on the web suggest https://github.com/andOTP/andOTP that unfortunately is not maintained anymore.
It seems that the code was created/maintained by a student that become busy at the end of his studies.
If you are still using andOTP I suggest that you migrate to a maintained App.
2FA and OTP, advantages and limits
If you are wondering what am I writing about here a quick overview of 2FA with OTP.
Two-factor authentication (2FA) with One-Time Password (OTP) is a security method that requires two different types of credentials to authenticate a user's identity.
It combines something the user knows (e.g., password) and something the user has (e.g., OTP token) to verify their identity.
Advantages of 2FA OTP
Increased Security: 2FA OTP provides an additional layer of security beyond just a password. Even if a hacker manages to obtain a user's password, they still cannot access the account without the OTP token.
Time-limited: One-Time Passwords have a limited lifespan, typically ranging from 30 seconds to a few minutes. This time limit ensures that the OTP can't be used again and again, making it more secure.
Easy to Use: OTPs are simple to use and require no technical expertise or additional hardware. Most OTPs can be generated using a smartphone app or sent via SMS, making it very accessible to users.
Customizable: OTPs can be customized to meet specific security requirements. For example, an OTP can be required for certain transactions or logins, while not for others.
Limits of 2FA OTP
Additional Steps: 2FA OTP adds an additional step to the authentication process, which may lead to frustration or confusion for some users.
OTPs can be stolen: While OTPs are more secure than passwords, they are still vulnerable to interception by attackers. For example, attackers could use phishing or other social engineering techniques to trick users into revealing their OTPs.
Smartphone dependency: If a user's mobile phone is lost, stolen, or damaged, they may not be able to access their accounts until they receive a new OTP.
Not foolproof: 2FA OTP is not a foolproof solution, and attackers can still find ways to circumvent it. For example, attackers can use SIM swap attacks to intercept OTPs sent via SMS.


